Security Hardening & SSL Setup
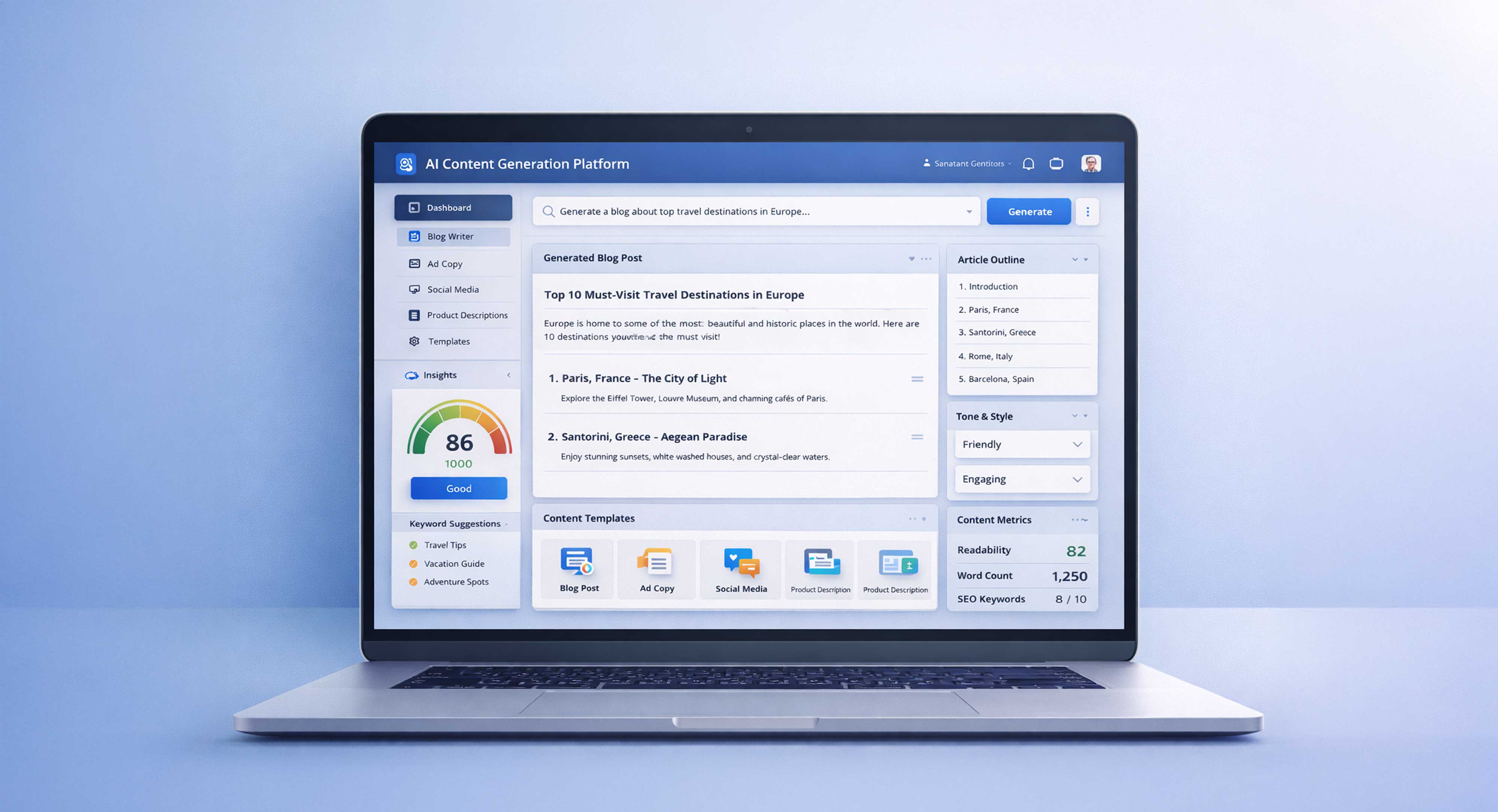
Protect Your Infrastructure with Advanced Security & Encrypted Communication
We implement security hardening and SSL setup to protect your servers, applications, and data from vulnerabilities, attacks, and unauthorized access.
Security Hardening & SSL Setup at M4YOURS IT focuses on securing your infrastructure, servers, and applications against potential threats and vulnerabilities. In today’s digital environment, security is not optional it is critical for protecting user data, maintaining trust, and ensuring system reliability.
We implement server hardening, firewall configuration, access control, secure authentication, and encryption practices to strengthen your system’s defense. Our SSL setup ensures encrypted communication between users and your application, protecting sensitive data such as login credentials, transactions, and personal information.
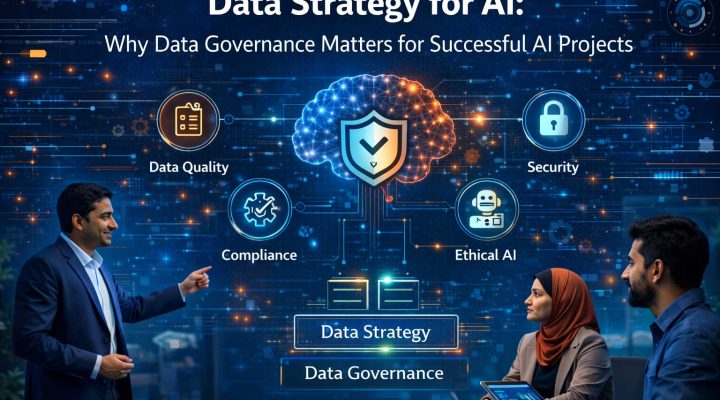
Many businesses face risks such as data breaches, unauthorized access, and insecure configurations. Our security solutions address these challenges by applying industry best practices, continuous monitoring, and secure configurations. Whether securing a new deployment or improving an existing system, we deliver robust, scalable, and reliable security infrastructure that supports long-term business stability and compliance.
Why Businesses Need Security Hardening & SSL Setup Service
Security threats, data breaches, and cyber attacks can severely impact business operations and user trust. Without proper security hardening and SSL encryption, systems remain vulnerable to unauthorized access and data theft. This service ensures secure server configuration, encrypted communication, and protection against common vulnerabilities. Businesses need strong security measures to safeguard data, maintain compliance, and ensure reliable operations. Investing in security hardening and SSL setup helps reduce risks, protect users, and build long-term credibility.
Key Benefits:
- Strong Server Security & Vulnerability Protection: Protect systems from unauthorized access, attacks, and security weaknesses through structured hardening practices.
- Secure Data Transmission with SSL Encryption: Ensure encrypted communication between users and servers to protect sensitive information and transactions.
- Reduced Risk of Cyber Attacks & Data Breaches: Implement proactive security measures to minimize exposure to threats and vulnerabilities.
- Compliance with Security Standards & Best Practices: Align infrastructure with industry security standards and regulatory requirements.
- Improved User Trust & Platform Credibility: Provide secure environments that increase user confidence and trust in your application.
- Continuous Security Monitoring & Risk Prevention: Detect and prevent security issues through ongoing monitoring and proactive updates.
[ Blog ]
Security
Insights, strategies, and best practices for securing servers, applications, and infrastructure with modern security techniques.
Security Hardening & SSL Services
M4YOURS IT provides complete security hardening and SSL setup services to protect infrastructure and ensure secure communication. We implement server security, firewall configuration, access control, SSL certificates, and encryption protocols. Our services include vulnerability assessment, secure configuration, authentication setup, and monitoring. We focus on delivering secure, scalable, and reliable systems that protect data and prevent unauthorized access. By applying industry best practices and modern security standards, we help businesses reduce risks, maintain compliance, and ensure safe, trustworthy digital environments for users and operations.
Server Security Hardening
We secure your servers by disabling unnecessary services, configuring firewalls, managing ports, and applying system-level protections. Our hardening approach reduces vulnerabilities, strengthens system defense, and ensures your infrastructure is protected against common attacks and unauthorized access attempts.

SSL Certificate Installation & Configuration
We install and configure SSL certificates to enable secure HTTPS communication between users and your application. This ensures data encryption, protects sensitive information, and improves trust, SEO ranking, and browser security compliance.
Firewall Setup & Network Security Configuration
We configure firewalls and network security rules to control traffic, block unauthorized access, and protect your infrastructure. This ensures only legitimate traffic is allowed while reducing exposure to threats.
Access Control & Authentication Security
We implement secure access control policies including user roles, permissions, SSH key authentication, and multi-factor authentication. This ensures only authorized users can access critical systems and resources.

Vulnerability Assessment & Security Fixes
We identify security gaps, misconfigurations, and potential vulnerabilities within your system and apply fixes to strengthen security posture and reduce risk exposure.

Security Monitoring & Threat Detection
We set up monitoring systems to track suspicious activity, detect threats, and respond quickly to potential security incidents, ensuring continuous protection.

Security Updates & Compliance Implementation
We apply regular security updates, patches, and compliance standards to ensure your infrastructure remains secure, updated, and aligned with industry best practices.
Our Security Implementation Process
We follow a structured and security-focused process to protect your infrastructure and applications. Our approach ensures vulnerability assessment, secure configuration, encryption implementation, and continuous monitoring while aligning with business requirements, compliance standards, and long-term security goals across servers, applications, and cloud environments.

Security Audit & Risk Assessment
We analyze your system, identify vulnerabilities, and assess potential security risks to define a clear security strategy and protection plan.
Security Architecture & Hardening Strategy
We design security configurations including firewall rules, access control, encryption, and system hardening for maximum protection.
Implementation & SSL Configuration
We implement security measures, configure servers, and install SSL certificates to ensure secure communication and system protection.
Testing, Validation & Security Optimization
We test security configurations, validate encryption, and optimize system defenses to ensure reliability and protection against threats.
Monitoring & Continuous Security Improvement
We monitor system activity, apply updates, and continuously improve security measures to maintain long-term protection and compliance.
[ Portfolio ]
Security
Explore our portfolio showcasing secure infrastructure setups, SSL implementations, and advanced protection strategies across modern applications.
Why Choose M4YOURS IT for Security Hardening & SSL Setup

M4YOURS IT delivers advanced security solutions focused on protection, reliability, and compliance. We combine technical expertise, structured hardening practices, and modern encryption standards to secure your infrastructure, reduce risks, and ensure safe, trustworthy digital environments that support long-term business growth and operational stability.
Key Reasons:
- Expert Security Engineers with Proven Infrastructure Protection Experience: Our team implements strong security measures using industry best practices and modern protection techniques.
- Comprehensive Server Hardening & Vulnerability Protection Approach: We secure systems against threats by eliminating vulnerabilities and strengthening configurations.
- Reliable SSL Setup for Secure Data Transmission: We ensure encrypted communication to protect user data and improve system trust.
- Strong Access Control & Authentication Security Implementation: We protect systems by enforcing strict user access and authentication policies.
- Proactive Threat Detection & Continuous Monitoring Capabilities: We identify and respond to potential security threats before they impact your system.
- End-to-End Security Setup & Ongoing Support Services: From audit to monitoring, we manage the complete security lifecycle effectively.
- Long-Term Security Stability & Compliance Focus: We maintain secure environments that align with industry standards and evolving threats.
Frequently Asked Questions
Security hardening is the process of strengthening servers, applications, and infrastructure by reducing vulnerabilities and applying secure configurations.
It includes disabling unnecessary services, configuring firewalls, enforcing access controls, and applying security best practices to protect systems from unauthorized access, cyber threats, and potential attacks.
SSL (Secure Sockets Layer) is a security protocol that encrypts data transmitted between users and servers.
It ensures that sensitive information such as login credentials, personal data, and payment details cannot be intercepted or accessed by unauthorized parties. SSL also improves website trust and is required for modern browser security standards.
SSL setup includes installing SSL certificates, configuring HTTPS, redirecting HTTP traffic, and ensuring secure communication across your application.
It also involves certificate validation, renewal setup, and performance optimization to ensure continuous secure data transmission.
Security hardening reduces the attack surface by eliminating vulnerabilities and enforcing strict security controls.
This includes secure configurations, restricted access, encryption, and monitoring, which collectively protect systems from threats such as hacking, malware, and unauthorized access.
Yes, we configure firewalls and implement access control policies to protect your infrastructure.
This ensures that only authorized users and traffic can access your systems while blocking malicious or unauthorized attempts.
Yes, we can analyze and secure existing systems by identifying vulnerabilities and applying security improvements.
We perform audits, fix misconfigurations, implement security controls, and upgrade existing setups to ensure better protection and reliability.
Security updates should be applied regularly to protect systems from new vulnerabilities and threats.
We recommend continuous monitoring and periodic updates to ensure your infrastructure remains secure and compliant with modern security standards.
Properly configured SSL has minimal impact on performance and can even improve it with modern optimization techniques.
With HTTP/2 and optimized configurations, secure websites can achieve fast loading speeds while maintaining encrypted communication.
Yes, we provide continuous monitoring, threat detection, and security updates to maintain system protection.
Our ongoing support ensures your infrastructure stays secure, updated, and resilient against evolving cyber threats.
You can start by contacting M4YOURS IT for a security assessment and consultation. We analyze your infrastructure, identify risks, and define a security strategy.
Based on this, we provide a detailed implementation plan including hardening, SSL setup, timeline, and cost estimation. Once approved, we proceed with secure deployment and ongoing support.
Secure Your Infrastructure with Confidence
Protect your servers, applications, and user data with advanced security hardening and SSL setup from M4YOURS IT.
We help you build secure, reliable, and compliant systems that reduce risk and increase user trust.
Start securing your system today.
Contact M4YOURS IT now and build a safe, future-ready digital environment.